Free Computer Studies Notes Form 1-4
Chapter 1
TABLE OF CONTENTS
Introduction to Computers
This chapter introduces the student to what a computer is, classifies computers into different categories, compares the different classes of computers and also introduces the keyboard as as a basic input device.
1.1 Definition of a computer
1.2 Classification of computers
1.2.1 Physical size
1.2.2 The way they process data
1.2.3 By purpose
1.2.4 By use
1.3 Acquisition of Keyboard skills
1.3.1 Layout of keyboard
1.3.2 Summary
1.3.3 Questions
Information is the result of processed data. For example adding some numerical values like the numbers 14 and 17 into the computer will give you the result of 31.
The later is information you required. Information can be defined as data computed into a more useful form than raw form.
Program is a series of instructions written in the language of the computer for them to obey and perform specific tasks as outlined by the instructions.
A Computer can therefore be defined as “an electronic machine that takes in data (facts) in the raw form, processes the data to give out in another form called information”.
When a computer is fed with data, it passes through four basic steps before the data can be displaced;
(i) Input Process — the user will type the data from say the keyboard (to be introduced later in the chapter)
and the computer will accept the dame and store within it.
(ii) Storage Process — the data that is fed into the computer at the same time is held, even during the time of processing and after processing; it can further be stored for further reference.
These data are held in computer memory.
(iii) Processing — the computer will manipulate the data held within it to a more useful form — results (information
(iv) Output process – the user is given the information he desired
The four basic processes can be summarized in the following way by looking at the same terms of information processing cycle.
Organizing data for processing — to get quality results (information) you must have quality data to start with. Unreliable original data generates unreliable results.
If you give a computer garbage, you get garbage in return. It’s called GIGO — Garbage In — Garbage Out.
Information Processing Cycle – Information Processing Cycle includes a series of steps for transforming data into meaningful information for people.
A cycle is defined as a sequence of activities performed in an order that it produces expected and meaningful results.
A Processing Cycle is repeated, it means, if the same resources are used in the same way, the same outcome will result.
The standard cycle followed to process data and deliver information comprises of 4 major functions:
(i) Input Function – the input function gathers and collects stored data items and enter them into the system for processing.
Input can come from many sources, for example from files kept in the office, banking institutions and accounts.
(ii) Storage Function — this function allows the user to store data being processed in the memory of the computer as well as to store the information for future use.
(iii) Processing Function — the desired operation by the user is carried out on the data keyed in and stored in the memory so as to turn it into meaningful information.
(iv) Output Function — the data stored is processed and then output into files, printed as hard copies or displayed on the screen for the user.
Note: For any information processing system to run smoothly on a day-to-day basis, the processing activities must be organized.
A system has little work if it provides helpful information on one day and useless information the next day. Output should be useful the first time and every time for the system.
1.2 Classification of Computers
There are four basic ways by which computers can be classified:
(i) Physical size i.e how large the computer is.
(ii) By the way they process data
(iii) By purpose
(iv) By use
1.2.1 Physical Size
The following computer systems are categorized by how large they are:
a) Monster Computer
Sometimes it is referred to as Super computers or Maxi computers. These are computers of enormous power and are very large in size. Its installation requires special floors to carry its weights and it also needs special plumbing to carry a fluid known as fluorocarbon needed to cool it.
One unique feature of maxi computers is that when you purchase it, the purchase price will include the services of 2 permanent engineers to maintain it forever.
They are typically used for scientific research and military applications, petroleum engineering, nuclear physics and meteorology.
Examples of monster computers include CYBER and CRAY computers. For example. the whole globe needs only one monster computer to forecast weather at once.
b) Mainframe Computers
Mainframe computers are second in size to monster computers. These computers perform more data processing work than any other type of computer.
For this reason they form a large portion of installation in most organization.
As does the monster computers, mainframe computers also have some special requirements, for the reason, they are housed in special rooms brought about by the special power that they posses together with environmental control requirements.
Mainframe computers can be used by more than one person at a time since they can support a large network of other computers organizations that employ mainframe computers alongside other computers are banks, government agencies, commercial and industrial agencies.
c) Minicomputer
Also called Medium sized computers. These computers compared to mainframe are smaller, slower and less expensive.
A minicomputer has an advantage over the previous two in the sense that it does not have any special power or environmental control requirements.
For this reason, the medium sized computer can always be located anywhere within the organization. Minicomputers can do the work that the mainframe does but on a small scale.
d) Microcomputers Of the types of computers, microcomputers are the slowest. However, they counteract this disadvantage because they are easy to use and the cost of purchase is also low.
A microcomputer gets its name from the fact that its main computing component, the microprocessor (to be introduced later) is located in one integrated circuit (IC) or what we call a Chip.
Microcomputers fit nicely on desktops, for that reason they are sometimes known as Desktop Computers.
They are also referred to as Personal Computers since many individuals purchase them for personal use.
1.2.2 Type of data processed
Classification of computers by the way they process data falls into 2 main types with the third being a combination of the two:
(i) Analog and
(ii) Digital Computers
(iii) Hybrid
(i) Analog Computers
These computers process data that vary continuously, for example variations in temperature, amount of current flowing through an electrical conductor and so on.
The flow of such data is in the form of wave like movement i.e. not predictable. Such computers are used for a wide variety of industrial and scientific applications that require the processing of data that are measured continuously. In conclusion, we say that analog computers measure things.
(ii) Digital Computers
As opposed to analog computers, these type count things. Data passed to a digital computer is usually operated on in steps i.e. form of discrete numbers, 0, 1, 2, 3, (a discrete operation). It is like counting on one’s fingers (1, 2, 3, 4…). Most computers in use today are digital.
This is because there are more counting applications than there are applications
than there are applications that requires continuous measurements
(iii) Hybrid Computers
These computers possess features of both digital and analog computers meaning both counting and measurement operations in one computer.
1.2.3 By Purpose Classification by purpose falls into 2 categories:
a) Special Purpose Computers
These are computers that are single task oriented. In other words, they are designed to solve only a particular type of problem.
Examples include embedded computers in our common digital watches.
b) General Purpose
Computers These are computers that can perform a vast number of operations or solve problems of different varieties.
Most of the computers in use today are general purpose. However, it is wise to note that general-purpose computers can always be adapted with special programs to do a job specified hence becoming a special purpose computer.
c) Embedded Computers
These are computers attached to other computers that help in operating them. E.g. computers embedded in lifts, petrol pumps, digital watches and so on.
1.2.4 By Use
It is worthy noting that we categorize these computers according to what it is used for and when it is used. Under this category, the list is endless. For this reason we will limit ourselves to only five main types.
(I) Personal Computers or Desktop Computers
These are also known as Microcomputers. They get their name from the fact that they fit nicely on the desktop. They can also be used on the desk in the office environment or for personal use at home.
(ii) Home based Computers
These computers are those designed to be used at home. An individual may install only games program in it or a word processor to enable them write letters, still some would install accounting packages to enable them budget and control their finances at home.
(iii) Laptop Computers
These computers get their name from the fact that you can place them on your laps while using. They are very small computers that have the structure of a briefcase i.e. you open and close the same way.
These have a keyboard attached to them and a flat screen together with a mouse ball and chargeable batteries. This means that you can use them in the rural areas where the is no electricity.
Laptop computers also have ports (small slots) through which you can attach an external keyboard, mouse or external drive like drive A:.
1.3 Acquisition of Keyboard Skills
There are many ways to enter data into the computer. However, the keyboard still remains the predominant input device for the many users.
A computers keyboard is used much like a typewriter keyboard. A keyboard has alphabetic, numeric, and special characters found on a typewriter.
The only difference is that data keyed in, is recorded in the computer systems’ data coding scheme and is stored in the memory.
The traditional format of a computer or terminal keyboard follows the organization prescribed by the typewriter keyboard.
This is known as QWERTY keyboard because of the sequence of the six letters on the upper left corner of the alphabet position of the typewriter keyboard.
1.3.1 Layout of Keyboard and Functions of Keys
A typical keyboard takes the form of a normal typewriter keyboard.
A keyboard usually has standard keys; that is letters of the alphabet plus special characters e.g„,,?, `, @ e.t.c. In addition to the standard keys, one finds a numeric keypad which is essential for applications that require entry of large amounts of numerical information.
Function Keys are identified as Fl through F12, they can be programmed to ease the work of frequently used operations. Cursor control keys of direction keys ) the ones with arrows, move the cursor on the CRT (screen).
Other special keys include: Delete keys and backspace keys which deletes characters. Delete key deletes a character that is in front of the cursor whereas backspace key delete characters before ti+cursor.
Insert key will insert characters from text. Others e.g home key will take you to the top of the document and end key to the end of the document.
Computer keyboard employ one or more control keys.
Control works just like the shift key on a keyboard in that they cause other keys to perform functions different from their normal operations. Example, if you hold shift key down and press the letter “e”, you get a different character “E”.
Holding down the control key while you press any of the other keys causes still another character to be sent to memory. Like the control keys, the escape key is used to cause other keys to perform special functions. Unlike the control keys, however, it is not held down while pressing another key.
Once sending_ a signal to the corn uter s stem for that cursor.
If you press another key following Escape, it will cause the computer to execute a function established by the program in use.

1.3.2 Summary
❖ A computer is a device that takes data in one form and processes it to give out in another form called information. + Data is the name given to facts. + Information is processed data.
❖ Program is a set of instructions written in the language of the computer indicating what the computer is to perform.
❖ 4 basic functions of a computer: Input, Storage, Processing and Output.
❖ Computers can be classified by: Size, The way they process data, By Purpose and by use.
❖ Typical keyboard is the same as a typewriter keyboard, has: standard keys, Numeric Keypad, Function keys, Cursor Control keys or Direction keys, Control Keys, Alternate keys, Escape keys e.t.c.
1.3.3 Questions:
i. Define a Computer.
ii. Differentiate between Data and Information.
iii. What is a Computer Program,
iv. What are the 4 basic functions a Computer will perform on data.
v. Discuss in detail how computers can be classified.
vi. Discuss the layout of a typical keyboard and functions of the different keys.
Chapter 2
Computer Components
This chapter introduces the student to the computer hardware system.
At the end of the chapter, the student should be able to:, differentiate between hardware and software, identify the elements of a computer systems’ hardware, explain the functional organization of the elements of a computer system, describe the central processing unit, describe the types of input and output devices, describe the types of secondary storage devices and media and finally be able to distinguish between system software and application software.
- Diagrammatic Representation of Divisions of a Cormputer System.
- Distinction between Hardware and Software.
- The Complete Computer System.
- Elements of a Computer Hardware System.
- Functional Organization of the Elements of a Computer System.
- Description of Central Processing Unit.
- Description of types of Input Devices.
- Description of types of Output Devices.
- Description of types of Secondary Storage Devices any Media.
- Distinction between System Software and Application Software.
- Summary. Questions..Diagrammatic Representation of Divisions of Computer
The following diagram shows the basic physical computer Breakdown that will serve as a reference throughout the chapter.
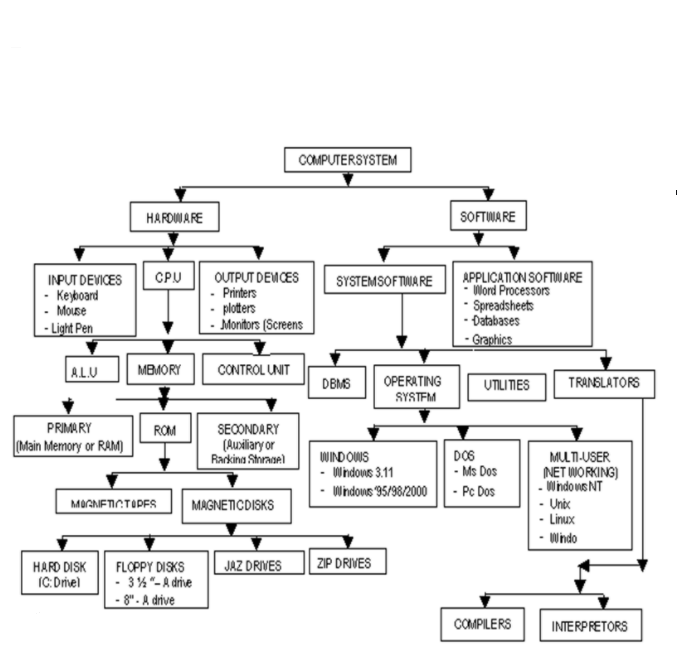
Key:C.P.0 – Central Processing Unit
A.L.0 – Arithmetic Logic Unit
DOS – Disk Operating System
ROM – Read Only Memory
RAM – Random Access Memory
DBMS- Data Base Management System
2.2 Distinction Between Hardware and Software
A Computer hardware from the simplest point of view is the physical or tangible parts of a computer whereas software are the intangible parts that help the computer to do its task.
From a technical standpoint, the following are the valid definitions and hence the distinction between the two terms.
A hardware is a name that describes all the electronic, electrical and mechanical components of a computer together with its peripheral devices.
software is the name that describes all the programs that are used to run the computer or do a specific task together with its documentation.
Explanation of the terms Peripheral devices referred to above are:
input devices e.g keyboard, mouse or output devices e.g monitor, printer.
These are devices that are used at the periphery or at the side or alongside the computer.
Documentation refers to, in its simplest form, the manual that helps the user to know how the different parts of the software work, how to install it, uninstall, trouble shoot or as a reference book. The definition of software is not complete until documentation is included.
2.3 The Complete Computer System
Because of the recent advances in hardware technology, people have thought of computers as hardware devices only.
This is far from the truth. The fact is,, the hardware is only one part of the complete system. Without programs to tell the computer what to do, they remain immobile and unproductive, just like an automobile without fuel.
A computer system is therefore defined as a combination of hardware devices and programs assembled to accomplish specific tasks. The broad categories of programs are often employed by computer’s operation. One category of program is known as Operating system.
As the name suggests, the operating system controls the basic aspects of the computer’s operation.
It is the driver of the computer.
The other category consists of the Application program which instructs the computer to perform those procedures necessary to get some jobs done; for example Word-processing, Accounting programs; as a group are often called Software.
Therefore, the three components of a complete computer system are: Hardware, the Operating System and Application Software.
The following diagram (fig. 2.3) shows the relationship between these three components.
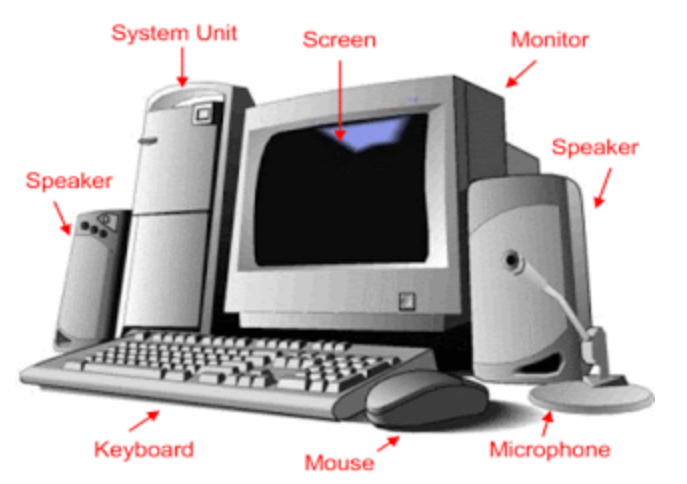
2.4 Elements of a Computer Hardware SystemThe hardware components of a computer system consist of a set of interconnected electronic and mechanical devices. All computing machines be it a calculator, a microcomputer or a mainframe has the same parts.
The parts of a hardware system are:
- Input devices e.g Keyboard,
- Output devices e.g Monitor, Printer and the Central Processing Unit which comprises of Control Unit (CU) and the Arithmetic Logic Unit (ALU) and Memory.The figure 2.5 shows the parts of a computer hardware system.
2.5 Functional Organizational of the Elements of a Computer SystemFig. 2.6 below shows the major physical components of a computer system
2.6 Description of the Central Processing UnitThe Central Processing Unit is the main component of a computer hardware system.
It is usually referred to as the CPU.
It consists of three parts. The main part of the CPU is the memory or primary storage, where data being processed and the programs controlling the computer are contained.
Arithmetic Logic Unit forms the second part of the CPU.
The ALU performs the calculations and makes comparisons between units of data.
The last component is the Control Unit (CU), the work of which is to control the operations of the hardware for example by issuing commands to all elements of the computer as per the dictations of memory. (e.g from the input devices to memory, from memory to output devices, etc).
The Central Processing Unit determines the power of a computer hardware system which is described in terms of :
(i) Size of Memory, which is measured by the number of characters of data it can store
(ii) Speed of the Control and Arithmetic Logic Unit, which is measured in millions of instructions per second (MIPS).
The work of the various input devices such as terminal keyboard, disk storage units and tape storage units is to send data into the CPU, whereas the work of the output devices such as printers, visual display units, disk and tape units is to give out the results from the processing operations.
The Central Processing Unit also “houses” Registers.
The latter is a small part in the CPU that holds data before processing or probably after.
They store data to be processed and thereafter partial results.
Registers are of different kinds performing different functions:
(i) Ordinary Counter Register (OC) – This register addresses the next instruction to be expected or we could say it contains the addresses of the next instruction to be executed.
(ii) Instruction Register (IR) – This register contains the actual instruction under execution.
(iii) Accumulator Register -This register stores data to be processed or the results of a partial execution.
The processor communicates with the main memory through 2 registers:
(a) Memory Address Register (MAR)
(b) Data Address Register (DAR) When reading a word from the memory, the CPU stores the address of that word in MAR and sends a read signal to a main memory.
After one memo M cycle, the value of the word is in DAR from where the CPU will search for it. When reading a word, the CPU stores in MAR the address of where the write operation will take place.
The value to be written will be stored in the DAR and then it sends the write signal to the memory.
Execution of an Instruction
The execution of an instruction of the central processing unit is performed through the following steps:
(i) Storage of the next instruction to be executed from the main memory to the instruction register (IR);
(ii) Modification of the contents of the OC registers the address of the next instruction;
(iii) Recording of the instruction recently stored;
(iv) Localization of the data needed by the instructions in the memory;
(v) Storage of data if necessary into the internal registers of the CPU generally the accumulator;
(vi) Execution of the instruction;
(vii) Storage of the results in the appropriate place;
(viii) Return to step () for the execution of the next instruction.
The Processor
The Control and Arithmetic/Logic Units are usually considered as a hardware device separate from the memory.
This is because the size of the memory may vary independently from the Control and Arithmetic/Logic Units.
As separate devices they are known as Processor.
Processors used in microcomputers are known as microprocessors (refer to chapter 1), but conceptually they are the same processors found in larger computer systems.
Memory
Memory A computer’s memory stores data before, during and after processing as well as the application program in use at the time.
These data are stored in cells of the memory. Each memory cell contains one byte of data (a byte = 8 characters: a character is say a letter of the alphabet, or a number).
Therefore, one cell will contain eight characters called a byte.
The size of the computer memory is measured in terms of “Kilobytes” or “Megabytes” or “Gigabytes”. Since “Kilo” stands for 1,000 and “Mega” for 1,000,000 computer memory is measured by the thousands or millions of bytes that can be stored in memory at one time.
In computer usage, the prefix “Kilo” actually stands for 1024 bytes and “Mega” for 1,048,576 bytes (explanation later in form 2 – Number systems).
Computer memory is sometimes known as Primary memory Storage, Main Memory and RAM (Random Access Memory).
Primary Memory
Primary storage or RAM is the computer’s working bench.
All data to be processed must first be recorded in it and all output of results draws data from it.
Primary storage has 2 crucial characteristics.
The first is that data can only be stored temporarily, and two, it cannot store a great deal of data.
Secondary Storage
These characteristics of primary storage give rise to the requirements to store large quantities of data in machine readable form that can be fed into RAM in small segments for processing. Units that do this are called secondary storage devices also referred to as Auxiliary Storage or Backing Storage.
. Description of these devices later in the chapter The two most prevalent of these are disks and magnetic tapes. These media offer the ability to store data offline, meaning that data can be processed from time to time by the computer system and are not stored permanently as part of the hardware configuration.
When needed, they are mounted on data reading and writing devices, called drops, as required by their application programs.
(i) The processor receives data from main storage, performs operations on them, then the result is given back to the same.
(ii) Data then goes to the main memory comes from input devices or secondary devices, and data from the main memory goes to backing storage or output devices.
(iii) The ALU and CU combine to form the processor as discussed.
2.7 Description of Types of Input Devices
Input devices in whatever form as the name suggests are devices that help the user to communicate with the computer by issuing commands in different ways which the computer obeys.
2.7.1 Keyboard
Please refer to 1.4 for full keyboard explanations. Using the keyboard is a matter of knowing which command you want to issue to the machine or what entries in the form of characters you want to make; then simply type in the right characters from the keys of the keyboard.
2.7.2 Mouse
This is another type of input device but as opposed to the keyboard, it doesn’t have keys. A mouse has usually two buttons (but not always).
When installed in your machine, a pointer is always seen on the screen. Underneath the mouse is a rotating ball which with the slight movement of the device on a pad, the pointer will correspondingly move on the screen by the same distance and to the right direction.
To issue an instruction to the system, the user simply needs to click (press the mouse button once – usually the left) a menu and choose a command he wishes to issue or click a command he would want to use.
You can use a mouse also to draw different shapes of your style apart from simply clicking commands.
A mouse (mice – plural) is usually employed in Windows Applications without which the Windows Operating System become incomplete.

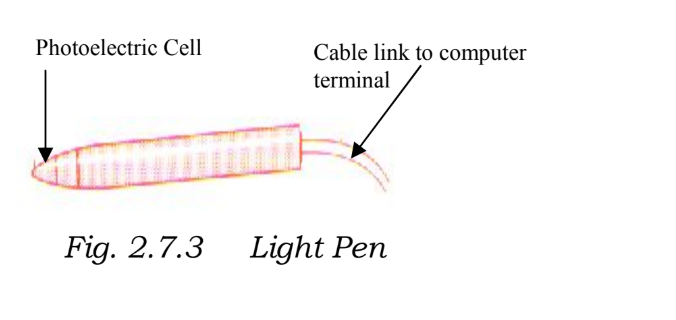
2.7.3 Light PensLooks like an ordinary pen but its tip is a light sensitive detector. When you touch the tip of the pen to the display screen, the computer locates what are called the x-y -ray coordinates of that point.
By touching the screen at various points, or by moving the pen across the surface of the screen, you can write and draw. Normally used with palm tops. Since palm tops are very small light pens replace mouse.
2.7.4 Joy StickThis is a device that permits you to move a picture, line, word, or cursor from point to point in a display screen. Used normally in playing computer games.

You operate a joystick by moving it in various directions. It carries out the same functions as the locate keys (cursor control) on the keyboard. But it is faster and lets you move in 8 directions instead of four.2.7.5 Graphic Tablet
It lets you draw a design just as you might do on paper. You use a special pen or your finger to do the drawing on a flat, table-like surface. Your drawing appears immediately on the display screen.
Laser ScannerThis input device is used to scan a picture or other documents from print onto the screen and hence can be available for storage in the computer memory for processing or future reference.
Some printers come with inbuilt scanners.
However, we have small scanners (manual) that are held in the hand while scanning an object to the monitor into the memory.
You can scan for example your photograph, signature and logo on other documents. Another scanner is known as a flat bed which is used by placing the document to be scanned on it.
2.7.7 Voice InputVoice input systems require that the user pronounce the vocabulary of voice command several times while the system does the “listening” and analyses the voice patterns of the various words. After this, using an airplay of the voice patterns, the system will respond to the commands as dictated.
Once the computer has been initialized with the voice pattern of the person, such a system will always not respond to anyone else. Example is voice dialing in a mobile phone.
2.7.8 Voice Input
Voice input systems require that the user pronounce the vocabulary of voice command several times while the system does the “listening” and analyses the voice patterns of the various words.
After this, using an airplay of the voice patterns, the system will respond to the commands as dictated. Once the computer has been initialized with the voice pattern of the person, such a system will always not respond to anyone else. Example is voice dialing in a mobile phone.
2.7.9 Optical Character Reader (OCR)
This device alone with others to be discussed shortly after, have been developed to make data input to computer s stenKleenc lerm Optical Character Readers (OCR) accept data input optically or with machines that respond to magnetic ink or magnetic Ink Character Reader (MICR).
2.7.10 Optical Mark Readers (OMR)
This device will place marks placed on forms for data gathering purposes. Such marks will then be translated into the computer by the device as input data.
2.7.11 Bar Code Readers (or Line Code Readers)
Bar Code Readers will read price and inventory codes printed on products that are frequently purchased such as in supermarkets. This code is usually referred to as Universal Product Code (UPC).
Such Bar Code Readers employed in supermarkets are one type of remote date entry terminals. They are known as Point-Of-Sale (POS) terminals. Remote data entry terminals promote entry of data directly into the computer system for the purpose of updating, inventing files and preparing customer’s bills and other similar tasks.
They are often used in manufacturing and distribution in warehouses, retail stores, bank teller counters and other business offices.
Workers and executors in the field usually use portable data entry terminal to enter and retrieve data directly into and from the main computer control via telephone lines.

2.7.12 Key to Tape / Key to DiskThis is a system of data entry normally employed when processing spiral documents usually in batches.
In any key to disk system, there must be a microcomputer that is used as the processing computer or server.
There will be a special computer terminal, each with a different operator in front of it Provision for a fixed disk drive where data is stored when keyed in is made, and finally there is a tape drive where after completing a given batch of data, then you re-locate. One of the terminals is usually dedicated for a supervisor to the system that oversees the whole operation.
2.7.13 Key to Disk
Operation Each operator loads the program usually employed to enable data entry of batches., then keys in the data from the original documents usually source documents.
The program in use will validate the data entry and incase of any error; this will be given on the screen and then will enable the operator to correct.
Once this is corrected, the data is stored on disk and the second operator is given the same source document to verify using the same process to the terminal and program.
Once a batch is verified as compact, the data is transferred from the disk to the tape drive and finally physically transferred to the server (minicomputer) for processing.
2.8 Description of Types of Output Devices
There are several output devices that are available within the current technological advancement. For our level, we will limit ourselves to the following: Printers, Monitors, Plotters, Sound Output and Microfiche /Microfilm devices.
2.8.1 Printers
Printers are necessary when hard copies of displayed work on the monitor have to be sent to customers, report prepared by the Management and the Board of Directors and so on must be printed.
It’s not disputable the fact that other electronic means of transmitting information are now available. Printed- paper, however, still remains the most popular means of communicating the same information.
Printers fall into three main categories classified by the amount of printed work the device is able to produce in one operation.
a) Page Printers These printers print a whole page at once. They are sometimes known as image printers.
They produce the images by laser or electrostatic means. The quality of output from such printers is sufficiently high for business correspondence.
They use toners just like a photocopy b) Line Printers
These printers produce a whole line of a text from before. They are very fast but the quality of the output is always low. It is important to note that the length of a line is not standard but different with the requirement of the application in use. However, most of the printers will print between 120 and 144 characters per line.
This will require approximately paper width of about 14 inches so as to accommodate the said character scale. 132 characters are often the most common width.
These use cartridges. c) Character Printers Form or print one character as a time on the• a er. This rate of printing varies between 20 and 600 characters per second depending on the mechanism or use in the • different makes employed.
These printers make use of ribbons. There are many different types of character printers.
The first is called Daisy Wheel Printer, which creates fully formed letters much like a typewriter sometimes called Letter Quality Printer. The output is often good enough for business correspondence.
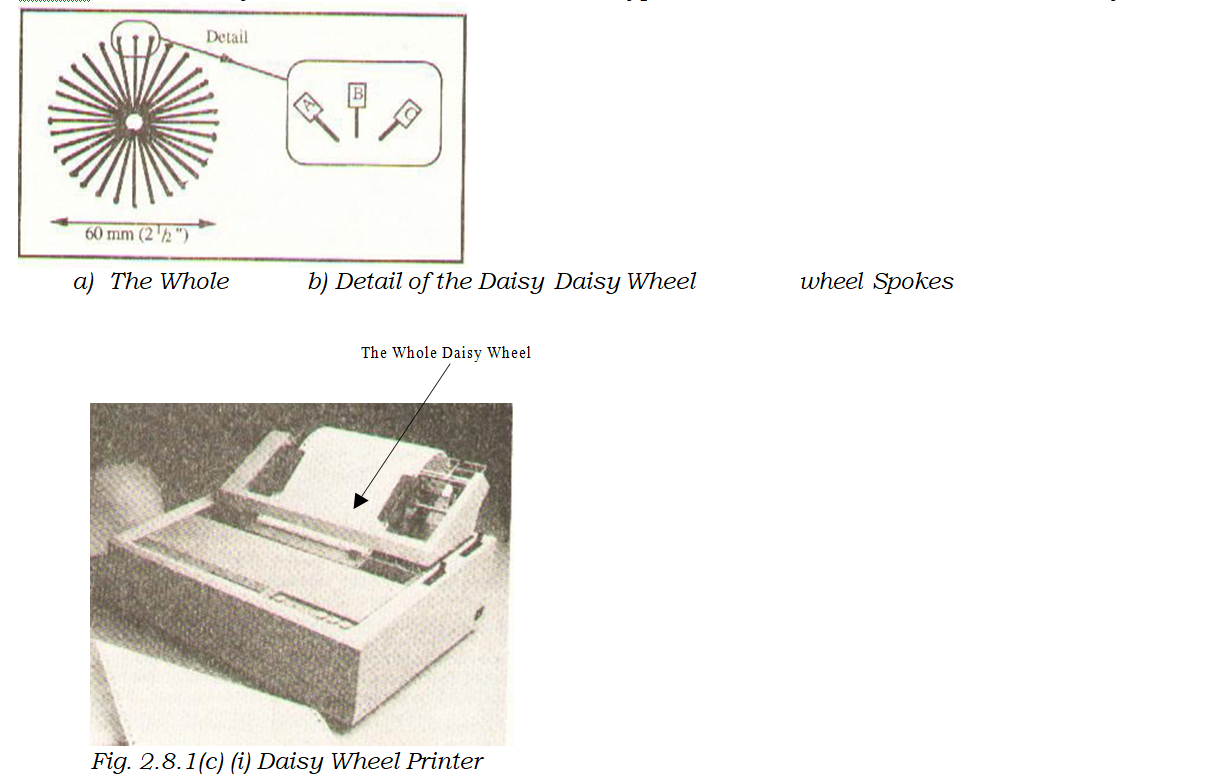
The second is Dot Matrix Printer, which creates characters as spools of dots in a rectangular matrix. The speed of the dot matrix printer is much higher than that of a daisy wheel but the quality of the former is not sufficient enough for business correspondence.A dot matrix printer has a print head consisting of a number of small pins between 9 and 24 depending on the make.
A printer with a 9 pin print will give a poor quality print compared to that of a 24 pin print head since the dots in the former are widely spaced apart.
If a dot matrix is to produce a better quality output, sometimes referred to as Near Letter Quality (NLQ), then a line is printed twice with the print head being moved along very slightly in the second printing so that those moved spaces between the dots are filled into ensure continuity.
One advantage with the dot matrix printers is that they can print from either side, meaning the print head does not have to move say to the left side of the paper in order to begin printing but begin from the right as well. With the dot matrix printer you simply need to change the ribbon of different colour to get a colored output.
How Character printer operates: A paper is passed through a printer that has a moving belt or a chain containing a complete character set – as seen from the keyboard. A paper is then hit from behind by a set of hammers, which are aligned for each printing position on the line. This will then pass a paper against an inked ribbon behind which is the character to be printed.Another way to categorize printers is by whether or not the print head strikes the paper. If it does, it is called Impact Printer and if it does not it is called a Non-Impact Printer.
Dot matrix and Daisy wheel printers fall in the former category; all strike the paper while printing.
Non-impact printers are usually the fastest since they minimize the amount of physical movement required during the printing process.
Examples of non-impact printers include Thermal Printers, Inkjet and Electrostatic Printers. Impact Printers are usually noisy given the physical motion involved during the printing process when the printing device strikes the paper.
To get multiple copies from impact printers, all you need to do is interlace a carbon paper between the papers.
How Non-Impact Printers worka) Thermal Printers
The slowest of all non-impact printers, form characters by burning them on specially treated paper. They operate at about 30 characters per second.
b) Electrostatic Printers
They form characters by charging the paper electrically. The paper is then passed through a toner solution.
Particles of the toner solution (ink) stick to the electrically charged areas of the paper.
When the paper is heated, the particles melt thus producing the characters. They are quite fast; some print about 300 pages per minute.
c) Ink Jet Printers
These printers “spit” streams of ink to the surface of the paper. The ink then drips almost immediately.
They are fairly slow. They produce from about 50 to 100 characters per second. These printers offset their relative disadvantage of slowness by their low cost and multiple colour printing.
2.8.2 Voice Output Computer voice output is commonplace. For example a computer could be programmed to offer telephone information service, like directory help. Others let you know if you dialed a wrong number or if the number you are calling is out of order or busy and the like.
2.8.3 Plotter
This is an output device used to produce graphical output like drawing graphs, charts, maps or electric circuits.
The design of the graph, circuit is done on the computer then the output is sent to the plotter.
Plotters are of two types: one that has a single sheet sometimes called Flat Set Plotter and the second uses a continuous sheet which rolls continuously on drum like cylinders: also known as Drum Plotters.
2.8.4 Microfiche/Microfilm
Microfiche and Microfilm are both better known collectively as microform.
The later is a document photographed and hence stored in a film. Microfiche is a sheet of film that measures 105mm x 148mm whereas a microfilm is actually a 16mm roll film.
A typical 16mm will hold the equivalent of 3,000 A4 Pages. One typical microfiche will hold the equivalent of about 98 A4 Pages.
Usually this technique of giving output to a microfilm/microfiche or microform is usually referred to as COM (Computer Output to a Microform).
The technique is simple, a machine called a microfilm Recorder reads output that is relayed onto a magnetic tape for the computer, once read, the output is copied out on microfilm/microfiche.
The application of COM is suitable where an organization has to store data over a long period of time or where backup copies need to be made.
Records that need to be out a long time would include: receipts and invoices of an organization or say catalogues in a library or a bookstore.
2.9 Description of Secondary Storage Devices and Media
As mentioned earlier, secondary storage or backing storage provide supplementary memory to main memory of the computer.
The following auxiliary media and devices will be discussed: Magnetic tape Drive and Magnetic Tape, Magnetic Disk Drive and Magnetic Disc, Magnetic Diskette Unit and Magnetic Diskette, Optical Disk Unit and Optical Disk, Mass Storage Devices and Media.
2.9.1 Magnetic Tape Drive and Magnetic Tape
The concept of storage in magnetic tape device used by computers is identical to tapes you may have in your home video or audiotapes recorder.
As a matter of fact, most microcomputers can use exactly these devices to store data. Magnetic tape consists of a large strip of plastic that has been coated with iron oxide compound that can be magnetized.
This strip is typically wound on a 101/2 inch for mainframe and microcomputer applications. Microcomputers employ audiotape cassettes. Data is recorded on and read from the tape using a tape drive.
The latter has a “read head” for reading the information stored on the tape that’s for transforming data from the tape into main memory. It also has a “write head” for recording the information. Usually, to read from, write to an individual tape, you have to mount it on a tape drive.
liuocsirit data is read from the ta e into main memo _oral )where the results are given out only as a written report or as another tape file written on another drive.
Because RAM capacity is limited, only a small amount of data is used for the input tape or written to the output device at one time.
Data that is stored on magnetic tape as well as other auxiliary storage devices are usually organized into records.
A record for now should be understood as a unit of data consisting of characters about someone or something. How data processing uses records is a matter of loading one or more records into RAM for an output device. Processing those records and sending the result to an output device.
This technique of sorting records on tape in the form of groups that are read into or written from RAM all at once giving rise to a number of technical terms that are used in all types of secondary storage media. See fig. 2.9.1 below.
A group of records is called Physical Records or Block. Each record in the group is known as a Logical Record. The number of logical records in a physical record is referred to as the Blocking Factor.A blocking factor of ten will indicate that ten logical records make up one physical record or block.
The term block refers to a group of logical records, all of which are read onto or written from RAM at once.
The physical records, or block, are suspended from each other by blank spaces on the tape known as Inter- record Gap (IRG).
Sometimes known as Interlock Gap:, Magnetic tape is a sequential medium, this means that records appear on it in sequential order for example personal records will appear by: employee number, account number and so on.
Because data is stored on tape sequentially, they must also be processed sequentially. If a tape file has only 60,000 records, access to record number 50,747 can be had only by reading through all of the proceeding 50,746 records. This is usually a very slow way of accessing data.
2.9.2 Magnetic Disk Drive and Magnetic Disk
Magnetic disk storage is the preferred medium for most secondary data storage today. As opposed to magnetic tape files, disk files need not be processed sequentially, although they may be if the application calls for it. Any record stored on disk may be retrieved without having top process through all of the proceeding records on the file. For this reason, a disk is usually referred to a Direct Access Storage Device (DASD).
This factor is what makes a magnetic disk faster and more flexible than the tape. Physically a magnetic tape consists of circular platters of non-magnetic such as aluminium and plastic, which is combined with the same sort of non- oxide coating used on magnetic tape.
As with, characters are recorded by magnetizing microscopic magnetic fluids on the disk surface using the usual data coding schemes.
Magnetization in one direction represents a zero in the other direction a one. To use a disk one has to mount it on a spindle that causes it to rotate.
A read/write head, similar to that of magnetic tape, moves back and forth across the disk radius rotating and storing data as required.
The read/write head can move to different sections of a record without necessarily having to write or read this section; only when the instruction was prompted! Disk Drive is the device on which the disk is mounted when used to store and retrieve data.
The device can position the read/write head in a number of portions along the disk radius.
As the disk rotates past the read/write head, data is recorded in a circular track. This means therefore, that there are as many concentric tracks displayed on the surface of the disk, as there are positions for the read/write head.
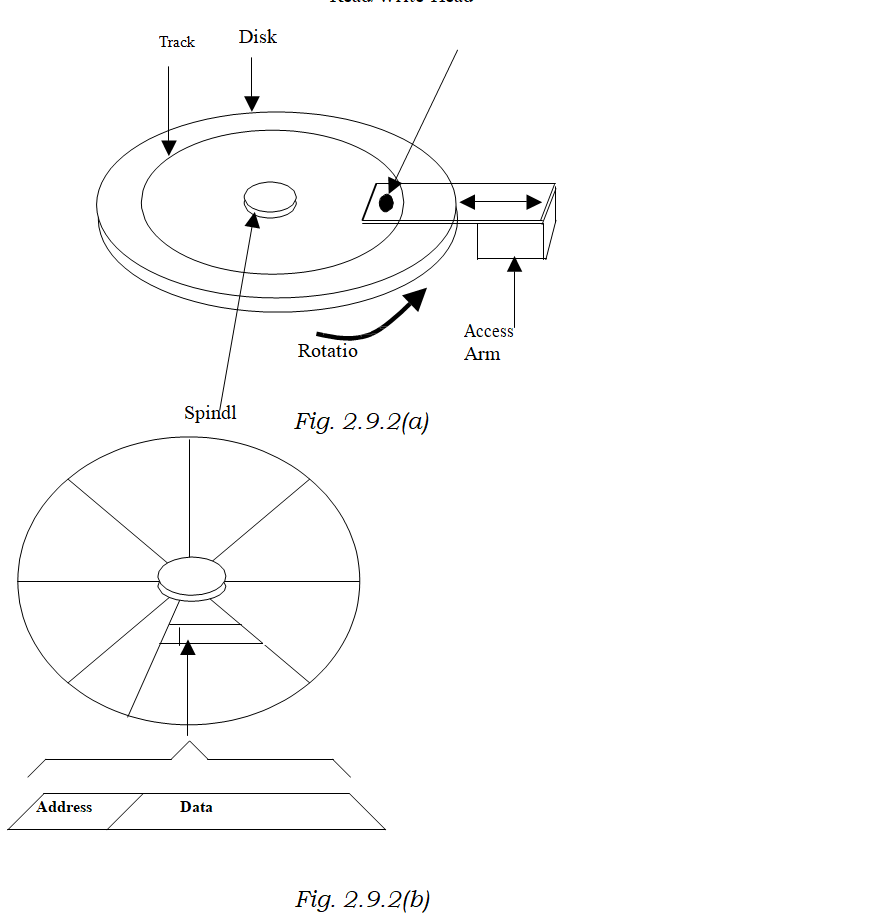
This is illustrated in Fig. 2.9.2 (a) Each track is divided into sections or blocks, similar to the blocks of data in magnetic tape.
Each sector has an address. To store/retrieve data, the system finds the disk address used to contain data by moving the read/write head to the appropriate track where it waits until the desired sector passes by. Fig. 2.9.2 (b) shows how a track is divided into sectors and how the sector contains an address used to locate where data is stored on the disk.
A hard disk with a capacity of 300k for example contains forty tracks (40) of nine sectors each; having a total of 360 sectors available on each side; of a two-sided disk for a total of 720 sectors.
Each sector contains 512 bytes or 4096 (512 x 8 characters, so the disk offers a total data storage capacity of 368,649-bytes. Such a disk is said to be a 360k disk following the conception that “k” equals 1,024 (360 x 1024= 368640). Read/Write Head
Disk storage media take different forms. Hard disks are rigid in nature. They contain the most data. Hard disks may be fixed in their devices or may be removed.They are usually 14″ in diameter, although it is unusual to the smaller hard disks in microcomputers. One such system is known as Winchester, so named because its prototype makes use of two drops of thirty million bytes each has effectively the “30-30″. It uses a 14″ plotter. Later versions called Mini-Winchester or Mini-winns” used 8″ or 6″ and one-quarter inch plotters, which are stored in the drives and can store up to 85,000,000 bytes.
2.9.3 Magnetic Diskette Unit and Magnetic Diskette
This is another form of disk storage media. Flexible disks or simply diskettes often called floppy disks or floppies because they use a thin sheet of plastic as their case. They are an important data storage medium for micro and mini computers. Diskettes ran:e in size from 3 1/2″ to 8″.
They offer the advantages of ease of transport and low cost.
They are encased permanently in a protective envelope, which is insulated in the disk drive.
The entrance to the drive is a narrow slot in front of the drive. This slot has a small flap over it, which must be clipped shut once the disk is inserted.
2.9.4 Optical Disk Unit and Optical Disk
Optical disk is a kind of audio compact disk or CD that you might have in your home. The device is made of plastic cover, which has transparent material.
The principle of work is the same as that of the CD; sound is recorded in them in digital form. Data is recorded beneath the transparent layer that covers the surface of the CD by burning a permanent pattern into the surface of the disk by means of a laser beam. Reading the data is also by a laser beam in an optical disk recorder.
The capacity of a CD is usually about (600 – 750MB). 1 Gigabyte, which is made up of 40,000 tracts each divided into 25 sectors. 1 GB is equal to 1 million characters-(1 GB). One advantage of CDs to magnetic disks is that losing data is not as rampant as with the latter. One disadvantage is that some (i.e CD-R) CDs are not reusable.
They are usually referred to as WORM, which stands for Write Once Read Many times. Reading from the CDs tends to be slower than that of the magnetic disks.
However, with the advert of CD- RW (Re-writable CDs) you can use a CD writer to delete obsolete work and write new data.
2.9.5 Mass Storage Media
A great need for machine-readable data storage in industries has prompted computer equipment manufacturers to develop storage devices with even higher capacities.
The top of the time disk unit manufactured by IBM doe example, stores more than 2.5 billion bytes of data. Data Car-tridge System stores data in a series of 50 MB cartridges. These devices provide up to half a million bytes of online storage.
The operation is similar to that of other secondary storage devices. A cartridge is loaded into the read/write mechanism, the data is processed and then the cartridge is replaced in its honeycomb-the storage bin.
Then the read/write mechanism moves onto finding the next catalogue to be processed. Cartridge systems are slower than disk systems because they involve more physical movements.
2.10 System Software and Application Software
System Software are programs with their associated documentations that control the entire operation of the computer.
It is what tells the computer what to do when you issue a command or when you switch on the computer.
Within the set of system software, we find a set of programs called Operating Systems.
The latter is usually defined as a set of programs that standardize the way a computer’s resources are made available to the user and to applications software.
The resources here refer to the hardware components of the computer.
The system software command imprinted on a type of memory called ROM (Read Only Memory). Such memories are usually reserved for such data of the operating system that the user must not modify or inadvertently delete.
It is usually protected by the manner in which it is manufactured.
ROM is used to store programs and data that are essential for the proper operation of the computer system and of the application program that are integral parts of the operation.
ROM is non – volatile; this means whatever is stored in such memory remains whether or not the power is on.
(RAM – discussed earlier is volatile). Programs such as operating systems and application programs stored in ROM are often called Firmware, meaning software that is engrained / fixed into the hardware.
System software also has what we refer to as Utility Programs for File management, editing files, management of disks and so on.
These are commands resident in system software. 2.10.2 Application Software This is a program that is usually applied on one area of operation only – not as all encompassing as system software.
Application software is usually divided into 2 categories:
(i) Standard Packages or Application Packages (General Application Software)
These are packages that are designed to be used to solve a particular type of problem for example Lotus 123, Ms Excel are all spreadsheet packages meant to be applied in accounting operation only.
Word perfect, Ms-Word are all word processors. D-base 4, Ms Access are database packages and so on.
(ii) User Developed Software (or Specialist Application Packages)
These are suites of programs with their associated documentation that are tailor made to solve specific tasks only.
Usually, a user will give a specification to a programmer of the suite he wants to be developed to meet his business or individual needs. This kind of software is only restricted to solving problems to which it is programmed to solve.
Tailor made software is sometimes known as Bespoke Packages.
2.11 Summary
- Computer Hardware is defined as all the electrical, electronic and mechanical components of the computer together with their devices used at the peripheral.
- Software are programs that are used to run the computer together with the associated documentation.
- Computer hardware comprises Input devices, Output devices and the Central Processing Unit.
- A complete computer system comprises the operating system, system software, application program and hardware.
- CPU is consisted of Arithmetic and Logic Unit which performs arithmetic and logic comparisons, the control unit which coordinates the activities of the hardware (I/O operations) as per the dictates of the memory, memory which stores data being processed, results and the application in use, registers which are slum areas in the CPU that holds data before processing and probably after.
- Storage Devices are in two forms: Primary Storage devices, the Main Memory and Secondary Storage devices which supplements the main memory.
- Storage Devices are in two forms: Primary Storage devices, the Main Memory and Secondary Storage devices which supplements the main memory. Q)
- Input devices include: Keyboard, mouse, paper scanner and magnetic ink holder. Other data capture methods include: speech, magnetic, optical character readers and optical mark reader.
- Output devices include: Printers – which could be line, page or character printers, they are also categorized by whether the print head strikes the paper while printing -impact and non-impact printers, visual display Unit, (or monitor) – displays the text/graphics for the user to see and plotters for plotting graphical output, electric circuits, charts etc.
- Secondary storage media and devices include: Magnetic tapes and disks, optical disks and mass storage media.
- System software are programs that control the entire operation of the computer together with the associated documentation. An application program is software that is usually applied on one area of operations only. They could be standard packages or user developed packages.2.11 Questions
1. Differentiate between hardware and software in a computer.
2. What does computer hardware consist of:
3. Discuss the functions of components of a computer hardware system.
4. A complete computer system comprises which components?
5. Discuss any 4 input devices.
6. Discuss any 4 output devices
7. What do you understand by secondary storage devices?
8. Discuss any three backing storage media and devices.
9. Distinguish between System Software and Application Software.
10. What is an Operating System?
11. What are Utilities?
12. What is Firmware?
13. What are the two types of Application Software? Discuss.
Chapter 3
Safe Use and Care of Computers
This chapter lets the student to be aware of the computer, its safety rules and how to apply them.
The safety rules to be observed regard personnel, materials and equipment in the computer laboratory.
The student is also expected to state correctly safety precautions required in the lab and be able to identify possible causes of loss of data and their precautions.
3.1 Behaviour in the Computer Lab.
3.2 Handling of Materials and Equipment.
3.3 Fire and Accidents.
3.4 Chemicals and Combustible Materials.
3.5 Ventilation in the Computer Lab.
3.6 Safety Precautions and Practices.
3.7 Possible Cause of Loss of Programs and Data.
3.8 Precautions.
3.9 Summary
3.9.1 Questions
13.1 Behaviour in the Computer Lab
Computer lab forms a very important section of an organization or school and therefore strict rules in terms of behaviour of personnel/students working/studying in the lab needs to be put in place and adhered to.
One factor to be taken into consideration is the cost involved in setting up the lab including the cost of equipment.
This should not be taken for granted and computers and other peripherals damaged in the short run could result in great losses to the organization. Cleanliness is a factor that stands out in the lab.
The personnel need to be clean while in the lab. Dust in the hands, oil on fingers is not allowed among personnel/students.
Foodstuffs to the lab is not allowed as the broken pieces from such will ultimately find their way into the peripherals e.g keyboards, disk drive and so on. Depending on what material cover is on the floor, certain shoes tend to cause a lot of distraction by making noise to the rest of the seated personnel.
This slows down the work process as attention will definitely be shifted. External disks into the lab are not recommended as this may result in virus infection to the system in the lab from outside sources Internal disks should not be allowed to leave the room.
Some stringent procedures should be laid down to check the personnel who ignore the rule. If this is not observed, it may lead to data from the organization being exposed to rivals or would be “hackers” – those who gain access to the system without authority.
Any mechanical or technical faults noted should always be reported to the technical personnel immediately for attention. Non-technical personnel should never attempt to deal with such a fault! It is important also that every personnel make routine backup copies of every work done in the lab as this will save the organization from any data loss in the event of disaster.
Shutting down and booting of computers is very important. Strict procedures depending on the operating system specification should be adhered to, otherwise damages to the disk in the long run and fragmentation of files and storage in the storage location will happen. This will cause delays in reading and writing to the same.
All equipment should not be moved around the lab rather they should always be used where they are installed! Changing of peripherals from one machine to another is not an encouraged practice.
Let a mouse meant for machine A remain the machine; if it does not work, please ask a technical personnel to attend to it, but do not interchange it with another!
13.2 Handling of Materials and Equipment
Handling of some materials and equipment in the lab should be a privilege.
In other words, some disks and special machines like a server (in the case of a network) should not be for everyone, only those authorized should be allowed for example to keep installation disks and so on.
Generally the computers and peripherals in the laboratory should always be handled with care since all of them have soldered electronic parts within them that when poorly handled and perhaps dropped then such parts will always either break or be dislocated. This will mean the equipment is damaged.
It is recommended that every movement to machines in the lab be done using a trolley.
No equipment should ever leave the lab unless with direct authority from the right person.
Computer cables should, if detached, be properly returned each to the right machine.
Technical operations in the lab should be left for only technical personnel. If every Tom, Dick and Harry in the lab assume to repair even damaged equipment, then more will be worse off than they were.
Disks should be kept from natural hazards like excessive temperatures, water and dust places and a way from magnets if data integrity is to be maintained.
13.3 Fire and Accidents
Fire and other accidents in the lab are Such accidents would include electrocution of an employee/student, slipping and falling on a slippery floor.
Fire is a big threat to data loss and equipment. Every lab should always offer training of how to handle fir in thee event of such calamity and of course fire-fighting equipment like fire extinguishers for example hand held CO2 and BCF extinguishers should always be available.
Data should also always be kept in fireproof safes to avoid loss of data loss in such event.
Insuring equipment and software in the organization with insurance firms will help since after such an accident, the firm is paid.
13.4 Chemicals and Combustible Material
Chemicals and combustible materials should always be located on special places. False floors and ceilings should always be available for chemicals like fluorocarbon fluid used as a cooling agent for mainframe.
Such pipes and ducts should pass either up on false ceilings or below false floors.
Combustible materials like fire extinguishers should be located in places visible to everyone but with strict instructions to be touched only in the event of a fire break out.
Other materials that could be harmful to the environment should be transmitted through properly located ducts.
13.5 Ventilation in the Computer Lab/working Area
Windows provide adequate ventilation in labs. Such windows must not be very wide as such will always be vulnerable to entry by intruders.
Any ventilation apart from the window should always be higher up and very small in size.
ventilation again, mostly windows, should have a well-dropped curtain so as to keep private the operations in the lab.
13.6 Safety Precautions and Practices
- 13.6.1 CablingCables in the lab should be properly located either on false floor or ceiling or along the walls so as to avoid interference for example with communication coolers in the lab.
Cables put haphazardly may result in possible power disconnection if stepped on or pushed around.
- 13.6.2 Stable Power SupplyProvision for stable, adequate and independent power supply is very important. Electricity suaci.p037m the com Aer syste,Interruption of power supply for example will damage disks, damage the processor and spikes will cause loss of data and fluctuations, voltage frequency will cut off other areas from the return.
As a precaution, large batteries, Uninterrupted Power Supply (UPS) and generators should always be on standby to such a crisis.
- 13.6.3BurglarProofing Counter All doors to the computer lab should be burglar proof. This is a physical security measure since this will avert any attempts by intruders to break in and interfere with data and equipment in the lab.
- 13.6.4 VentilationIt is a good practice to include ventilation in a computer room but the same should not provide an entrance to hackers to tamper with data.
- 13.6.5 Floor spaceThe space on the floor should be wide enough to provide a thorough route for equipment installation and other movements of the trolley to transfer equipment. It should also provide for an emergency exit.
NB: Slippery floors are not recommended in a computer lab. Such a floor if there is should be covered with mats and the like.
Vdu Legislation
This is a legislation (British) that was passed in 1990 for frequent users of computer screens in the lab.
It states as follows:
1. One should not use a computer for more than one hour continuously.
2. While using the VDU, the eyes should not look at the screen directly but at an angle of 30°-60°.
3. The distance from the screen should be between 300mm-480mm.
4. While using the keyboard, the arms and elbows should be at right angles and parallel to the ground.
5. The seats and desks in the lab should be adjustable to the users height this is to aid (iv) and avoid Repetitive Strains Injuries (RSI) of the fingers and wrists. The seats should have backrests!
6. All seats in the lab should be fitted with castors – to make them mobile and less noisy.
NB: An Anti-glare screen is still recommended.
Computer Lab Design
Before we look at the safety regulations in the lab, it is vital to look at what factors must be put into consideration when designing a computer room.
Constraints of Computer Room
- The following requirements must be observed in any computer room design:
- The need for air conditioning The dimensions of size of the lab
- The need to observe cleanliness Equipment sitting in the lab
- Accessibility for machinery maintenance and media re-supply.
- Consideration for health and safety
- Consideration for noiseAir Conditioning
Air conditioning is very essential in the computer room where main frames are housed or some minicomputers together with their associated peripherals.
Most devices however, usually contain their own environmental controls that are automatic for example fans, filters and sealed units.
Air conditioning is done to enable control the following:
(i) Temperature – for equipment should be between 18°C and 24°C.
(ii) Humidity – this helps to avoid moisture precipitation and build up of electrostatic charges. Recommended humility should be 45% – 55%.
(iii) Dust control – disk media require high level of cleanliness.
Processors with highly packed electronics require high levels of cleanliness. To help keep a high level of cleanliness, the lab should have positive pressure, air lock and sticking nuts on the floors.
Dimensions of the Lab
The size of the computer room should take into account the following:
• Requirements specified by the equipment supplier
• Operating conditions and
• The need for future expansion.
• The height should be enough to provide for false floors and ceiling to help spread equipment loads provide safe cable paths and air ducts.
Accessibility
While installing equipment in the lab, there must be a provision for a through route, which is also important for emergency exit.
Only for security purposes should such a route be closed.
Corridors of the lab must be high enough with double doors and floors, stairs or lifts must be strong enough t bear the load of equipment.
It is often recommended that ground floor should be used but this again has many security risks.
Reception should always be spacious enough to allow for storage of trolleys (used for moving equipment around the lab).
Equipment Sitting Design of the sitting equipment should always be such that it ensures the workflow of the operator and minimizes the walking distance from one…end to another.
This means for example that the location of a stand-alone computer and the printer should be close enough to ease the work!
Health and Safety
For the sake of health and safety of the staff and equipment, the following should be observed:
a) Lighting
There should be a provision for large lighting so as to avoid minimized reflections and glare.
A further provision should be for emergency lighting.
b) Alarms Fire alarms in the lab must be very clear (audible) and visible from any angle you are placed. This will allow for quick action and reaction in the event of a fire break out.
c) Communications To avoid noise in the lab, telephone lines should be strategically placed with visible indicators for quick response.
d) Physical security General:
• Only authorized personnel should be allowed into the computer room.
• The lab should not have any outside walls to keep off intruders.
• The lab should have small windows’ provision for ventilation.
• Video cameras should be on to monitor the activities of the personnel and intruders.
e) Fire Alarms
should be in place as discussed earlier. Automatic detection of smoke and electrocuting systems should be provided for. In the computer room, there should be hand held Coe and BCF extinguishers. The personnel should be given evacuation training in the event of the fire break out.
f) Flooding Computer labs should never be sited in basements where they are vulnerable to floods. No water pipes should be placed under, over or in the computer rooms.
This is because water is likely to destroy equipment, programs and data in the lab.
g) Power
The computer room should have independent power supply, stable and adequate with shrouded panic off button.
Problems with power supply come in three main forms:
(i) Supply interruption – is caused by a number of factors that include transformer failure, cutting of supply lines by accident, by people, lightening and so on.
(ii) Spike – this is a voltage level imposed onto the supply by interface source such as switches, electro-mechanical devices and so on. The problem caused by spikes is generally loss of data as soon as power is removed. Disk files also get corrupted when store cycles are interrupted by removal of power.
(iii) Voltage Frequency Variation – this is variation or fluctuation in the voltage frequency of electricity supply.
Such fluctuations normally do not have effect since in most computers, there are power supply units that are designed to adequately cope with any small fluctuations Problems caused by voltage frequency variations is generally loss of users in the sense that terminal links get broken in those parts of a network whose power is interrupted or destroyed. So this problem is normally experienced when computers are networked. When designing a computer lab, it is important to have a standby generator, large batteries or other uninterrupted power supply (UPS) units so that in the event of power failure, the data is not lost, or users disconnected or disk media damaged etc.
13.6.6Dust/Dump
Proof Disk storage media and processor require a high level of cleanliness and standard temperature in order to maintain the data stored and of course for power to adequately function.
The lab should therefore have a positive pressure, suitable building materials to reduce dust,special floor covering to reduce the dampness and so on.
13.6.7 Lighting
The computer lab should have adequate lighting. This lighting should be large enough to minimize reflections and glare on the part of the user. There should also be a provision for emergency lighting.
13.6.8 Standard Furniture
The furniture used in the lab, that is the table on which the machine is placed should be stable and firm with enough room under for the user’s legs and clearance to allow posture changes.
The surface of the desk should be spacious enough to allow flexible arrangements of items, it should be glare free. The chair should be adjustable to allow different personnel of different heights to use the desk.
13.6.9 Fire
Fighting Equipment Provision for the fighting equipment in the lab is vital.
Fire extinguishers like hand held BCF and CO2 extinguishers should never miss.
Supply equipment should always be located in visible places for staffs.
More important is the adequate training of how to handle such equipment and precaution techniques for the personnel.
13.7 Possible Causes of Loss of Programs and Data
Loss of programs and data to the organization results in loss of information that may not be put in monetary value. Some of the causes include:
13.7.1 Power Supply Power supply problem result in two forms:
- Power supply interruption – is one form which can be caused by transformer failure, cutting of supply lines, by accident, by people, lightening and the like, inadvertent switching off of the machine also could interrupt power supply.
- Spike – is the second form of power supply problem, this is a situation where a voltage level is imposed onto the supply by interference source such as switches, electro mechanical devices and so on.All these forms of power problems especially supply interruption and spikes result in damage to disk heads which often crush when power is suddenly removed.
This will mean loss of data since it will be hard to read or write to such a disk.
Spikes often result in serious loss of data since RAM being volatile losses data immediately power supply is cut off.
Disk files also get crumpled when stores are interrupted by removal of power.
13.7.2 Virus
A virus is a peace of software (program) that replicates itself without the user intending it or noticing it Viruses often affect our computers having been brought about by hardware/software engineers who move from one computer to another carrying out demonstrations or through external infected disks, which are brought into the lab.
Such disks are often infected with boot sector virus (boot sector is the first partition of the hard disk/floppy).
When it (infected disk) is put into the drive, it will be loaded into memory. The disk is now infected since the memory to which it must be loaded first is now infected.
A virus usually has many effects for example replication where a virus divides itself repeatedly thus spoiling the data on the screen/memory/or disk.
Viruses have so many effects they cause to data/information and to the user.
What we need to note here is simply the fact that viruses will change or modify the data that was stored to take a different format that is never useful to the operator.
13.7.3 Accidental
Erasure It is possible that the user without him wanting it could erroneously erase data. This usually comes about for instance while using a delete command say in Ms – Dos(next chapter), one happens to delete a whole directory while the intention was to delete a single file in the directory.
As will happen,, one uses a disk command like disk copy without identifying the source diskette from the destination disk.
If the two are mixed, then it is possible to wipe the contents of the source disks erroneously.
13.7.4 Crashing
Disks Disk heads, as mentioned earlier, often crush when there is sudden power supply disconnection. Data is often lost since reading from one disk and writing to them is not possible. This means that data in that disk was lost.
13.7. 5 Poor Storage of Disks
We said that the disks require very high levels of cleanliness above any other. Dusts will clog the disk head.
That causes a problem in reading and writing to the disk. Storing disks in dump places and very dry places have effects on the disks, the surface will either become too delicate or fold away from its shape.
All these minimize the reading and writing processes to data in the disk.
13.7. 6 Unauthorized Access
Only authorized personnel should always be allowed into the lab.
It is possible that hackers could gain access to the room and “steal” data/information, which could be tampered with in some way or even a virus infected into the system.
Also unauthorized persons could perform some fraud with the data for say personal gain at the expense of the organization.
A hacker could gain access to for example change an existing invoice to reflect a higher or lower bill, clear an invoice, etc.
13.8 Precautions
The following precautions should be put in place to avert the possible loss of data through the risks identified above.
13.8.1 a) Power Failure
Power failure is a risk to data in the organizations. Precautions to be taken include:
b) Regular Saving of Documents/Files
The user of the system should always ensure that the work is saved as regularly as possible, say after every automatically for the user.
If you don’t save your work periodically, then any power interruption/spike will mean all the
c) Use of UPS
UPS in short for Interrupted Power Supply, This is a simple device that consists of suitable sized strapped capacity of the system it is required to support and for how long. This method can be interrupt driven from a simple 5 to 10 minutes.
Some applications will always do this work you did and will be lost. across the input supply.
Its size is dependent upon the hardware dictation circuit which automatically locks the user out as soon as an interruption is detected and all data is automatically stored and also safely packed before the system is switched off.
d) Use of Batteries and Generators
Standby generator systems together with large batteries are necessary to sustain the continuity of computer facilities in such organizations as hospitals, military installations, factories and some offices.
In the event of power interruption, what happens is that the system is first maintained by the battery while the generator is started up.
13.8.2 Virus
The following precautions should be adhered to so as to guard against virus: a) Write Protection Disks Every floppy 31/2 disk contains a physical write protect tab on the left hand corner that slides down to indicate its “on”.
When the disk is write protected, it means you cannot be able to write anything or change a word in it, you can only read! This will protect you against virus since it cannot allow any external data of any form!
b) Restriction of Disk Movement
Strict procedures should always be put in place and adhered to by all IT staff. Such software will ask the user to “repair” hard disks and floppies as well as the boot sector from viruses.
Such a procedure should be for the sake of data integrity, no disk from the organization should leave the computer room and at the same time any external disk should not be used in the system unless “sheep dipping” is carried out.
The term simply means scanning the disk for viruses first before being used.>
c) Disable Disk Drives
Another viable alternative to virus protection would be to physically remove all the disk drives once the normal working hours are over. This should be done by the technical staff only.
When this is done, it means that even if you had your disk to use you cannot because the disk drive to let you read and write to the disk is not there. This will help protect the organization against boor sector virus and the like.
d) Anti Virus Software
Software are available in the market today that help to disinfect diskettes (disks) and of course the main memory from the virus infection.
Since new viruses come up often, it is always recommended that such software installed into your system should be regularly updated or a newer more powerful one installed.
Such software is often easy to use once installed. Examples of such software include: Norton Anti- virus, Dr. Solomon Anti-virus Tool Kit, F-Prot Professional etc.
Such software will scan and ask the user to “repair” hard disks and floppies as well as the boot sector from viruses.
13.8.3 Accidental Erasure
When a file, document, software is accidentally erased, it is possible that you can put in place some recovery procedures provided for in the form of utilities by the operating software.
Depending on the operating system in use, and the application software, the user can be able to un delete an “already deleted file” or document by simply evoking the utility.
If the data was lost as a result of formatting a disk, a utility to un format the same could be provided. These utilities will therefore help to recover such accidental lost data.
Another precaution to put in place would always be to use backup copies of the information lost. A backup copy is simply the alternative copy that was made of the information contained in a particular disk.
This as the explanation states will help the organization to continue working without any hitches. Another option is to use fireproof safes (heat- resistant safes).
Heat is a threat to backup copies made on diskettes. Diskettes tend to fold under excessive heat.
To avoid the loss of data in this way, it is recommended that such disks be kept in heat resistant safe always.
13.8.4 Crashing Disks
Power interruption, we said, causes the disk heads to crash. This causes a problem in reading and writing to the same disks.
A precaution here would be to use backup copies of the same disks in the event of such a crash. To avoid such a crash, it would be important to observe precautions for power failure.
13.8. 5 Poor Storage and Handling Disks
Disks are very sensitive storage media and a lot of care needs to be taken to ensure that the data/information stored in them is safe and that the disk can be read and written to. Most floppy disks are covered by plastic material which react easily to excessive temperatures like direct sunlight or very cold dump situations.
Therefore, to preserve the disks, keep them away from sunlight as this is likely to cover the plastic envelope covering the disk which will ultimately affect reading and writing; keep them away from water which would make the disk surface dump and hence affect the storage layers (sectors, tracks and cylinders) where data is stored.
Disks should also be kept away from dust environment, as those again will make the disk drive heads.
This will cause loss of data if the disk heads cannot read and write.
The mode of storage to these magnetic disks is by magnetism of the positive and the negative charges of the data to be stored.
If disks are kept next to magnets, it is possible that the demagnetization of this sequence could be altered. This will of course destroy the data stored in the disk.
13.8.6 Unauthorized Access
Access to the computer room should be a privilege. Only those personnel working there should be allowed in. when access to the lab is not restricted, then it becomes easy for hackers to gain access to the system and hence destroy or “steal” information.
Fraudulent activities lem akin: confidential information to rivals for .a ment is also possible. Other intruders could also gain access to the system and hence destroy or carry out ridiculous acts like literally stealing the equipment.
Some files attributes should also be put in place to avert access to data stored. For example, the use of passwords should be encouraged; data encryption method should also be adopted.
Passwords could be a number(s) or a word that is only known to one person or some “trusted” personnel in a department or a sector that will enable the user to gain access to the system or a particular document or file.
The use of passwords will ensure that only those people who know the password could gain access to those files in the system.
Passwords if to be used should always be changed periodically in case it has been leaked to someone who is not authorized to know it.
Data encryption is a way of writing a particular information using a given grid that could only be deciphered by you or a group of personnel authorized to for example: to encrypt the following statement in a 5 x 4 grid (i.e a row is 5 and a column is 4 letters) would be:
The statement: MEET TO NIGHT AT 8PM
MEET.TO . NIGHT . AT . 8.PM
The statement to be stored as data is MMN.EEIAE.GTTTHt.OT8
The statement LICENCED TO KILL could be encrypted as LCOLIE..CDK.E.I.NTL. in a 5 x 4 grid i.e. LICEN LICENCED.T O.KILL NB: Note that a word to be encrypted in full as you move along the row. Separate each space by a dot. To read, read the first letter in the first column and move down the column. Each dot is a space.
13.9 Summary
Factors to consider when designing a computer lab are the following: Dimension, accessibility, sitting of equipment, health and safety of personnel, lighting, power supply, physical security and noise.
Strict rules to the lab concerning behaviour as outlined should be observed.
For safety precautions on the lab, the following should always be considered: Fire fi htin equipment, standard furniture, proper lighting, dust/dump-proof lab, proper installations, stale power supply and burglarproof doors.
Possible causes of data loss and programs are the following: power failure, viruses, accidental erasure, erasing of disks, poor storage and handling of disks and unauthorized access by hackers and other intruders.
The following are precautions to be taken in the event of data loss from such risks mentioned.
■ Use UPS, large batteries and generators in the event of power failure.
■ Use of anti virus software, write protecting disks.
■ Movement restrictions.
■ Disabling disk drives to protect against viruses or accidental erasure.
■ Use of undeleted and unformatted utilities.
■ Use of backup copies and heat resistant safes.
■ Disks should be stored away from water, fire or excessive temperatures and away from magnets and should be kept in dust free environments.
■ Use of passwords and encryption methods to protect files against unauthorized access by people.
13.10 Questions
Operating Systems
This chapter will introduce the student to what operating terms are the functions and types. It will also serve to explain how disk Operating System (DOS) organizes information. The student is expected to use some DOS commands for file and disk management and be able to list external and internal DOS commands at the end of the chapter.
4.1 Definition of the term Operating System.
4.2 Functions of Operating System.
4.3 Types of Operating Systems.
4.4 How DOS organizes information.
4.5 List of DOS commands.
4.6 File Management Commands.
4.7 Disk Management Commands.
4.8 Summary.
4.9 Questions.
4.1 Definition of the Term: `operating System
Operating System as defined earlier, is a set of programs available within the system software that standardizes the way a computer’s resources are made available to the user and to applications software.
4.2 Functions of an Operating System
The following functions are identified as common to all Operating Systems:
4.2.1 Memory Management
An Operating System allocates memory to itself and to its resident system programs, sets aside areas of application programs and user partitions, arranges the input and output buffers (areas on RAM where input data and output data are temporarily stored) and reserves storage for specialized purposes.
4.2.2 Input/Output (I/O) Management
The Operating System controls reading of data coming in from the various input devices into the memory and writing of data to output devices such as printers.
The Operating System will ensure that each time the user types in commands those inputs are accepted into the memory, and if the latter is busy the it holds the same temporarily on buffers until the memory is free and also does the same to output data awaiting to be displayed on the monitor or to be sent to the printer if the same are busy.
4.2.3 Resource Allocation
Operating System load programs into the computer memory and starts them running after receiving instructions from the user, at the same time, operating systems must have ability to divide resources available to different users, memory and of course the peripherals to different processors going on at the same time so that none of the users gets “stuck” or “deadlocked” during the operation for lack of a computer resource.
4.2.4 Error Handling
Any Operating System must have the ability to handle errors in the computer system be it hardware or software faults and be able to provide routines to correct these errors.
4.2.5 Provision for User
Interface Any Operating System should have the ability to receive commands from the user and respond to them accordingly.
4.2.6 Interrupt Handling
An interruption could be caused by software errors, mechanical faults of a machine or by the operator by pressing the Break key for example which halts the system. The operating system should always be able to handle such interrupts without causing any malfunctions as a result.
4.3 Types of Operating Systems
There are majorly two types of Operating Systems that we will discuss in this section.
4.3.1 Single User System
In this type of Operating System, only one user can use the machine at a time, load one program at a time in the main memory and process only that one program. Most of the small microcomputers employ single user systems. Examples are Ms-DOS, Pc-DOS and Windows.
4.3.2 Multi User System
This system as the name suggests is for multi user, as opposed to the single user system.
This system is employed by Agency microcomputers and minicomputers. More than one program can be loaded into the main memory by different users and processed at the same time in an interactive manner. Examples of such an operating system are UNIX and Windows NT.
4.4 File Management
Medium of storage employed by most microcomputers is often disk. Data that is stored on disks are often held in a file.
The latter is often referred to as a group of related records. The records may hold data about customers, employees of the organization and names of students in a school and the like depending on the organizations.
Therefore, the file as a group of program instructions is actually a computer program. When files are stored on such storage media, then the term “file” refers to anything stored on the medium, be it a program or data file.
4.4.1 File and Directories
The work of the Operating System is to keep or maintain a directory of the address of the files on disk. Each file on the storage media is assigned a name called filename (one word).
The directory is a list of filenames and the disk addresses at which the file may be found. When the user refers to a particular filename, it causes the operating system to consult its directory of filenames, locate the address of the required file and make it ready for use. Let us have a look at a directory listing of files of a system disk using Ms DOS.
All of the files in this directory are programs.
A system disk is so called because it contains the directory system. We shall list directory for system drive A: Volume in drive A: has no label.
Directory of A: COMMAND COM 18107 13-12-97 13.00PM SYS COM 7407 13-12-97 13.00PM DIRECTORY COM 1307 13-12-97 13.00PM FIND EXE 1278 13-12-97 13.00PM 4 FILE(S) 142890 BYTES FREE
What the list shows:
(i) the name of the file e.g. COMMAND
(ii) Filename extension e.g. COM
(iii) The number of bytes contained in this file
(iv) Date and time on which it was printed into the directory.
(v) The total figure at the bottom of this directory listing show the number of bytes remaining for storing other files. MS-DOS has certain rules for formation of filenames for example; A filename must not exceed 8 characters in length and in some cases requires filename extensions, which is 3- character in addition to the filename.
In the above example, COM and EXE are extensions. Although not visible, there is usually a full stop between the filename and the extension e.g. Diskcopy.COM is the complete name for the above file.
The user has to type in the computer name of the file including the period in order to effectively use some file maintenance utilities like copying or deleting. Filename extensions usually indicate the type of file for example “COM” and ti3XE” above will refer to program files.
4.4.2 Directory Hierarchy
Files stored on a disk can always be organized into subdirectories.
Directory hierarchy refers to a “tree” like structure formed by directory -subdirectories – files. For example, we could have a directory called KENYA with subdirectories of towns NAIROBI, MOMBASA, NAKURU and files of Estates within each town, e.g. Hurlinghum, Nyali and Milimani. The figure below shows the directory hierarchy.
To be able to specify which file to open, the user has to specify to the operating system the data path or path to that file. For example, to open a filename Milimani, the following path must be specified: Kenya \ Nakuru \ Milimani.
A path is often defined as a logical, sequential list of directories and subdirectories leading to a filename. The names of directories and subdirectories are separated from each other by determinates which could be a backslash(\) or a hyphen (-) or a slash (/) depending on the Ms-Dos version in use. The directory names have extension DIR wheras the files have TXT.
The directory named Kenya under which the subdirectories Nakuru, Mombasa and Nairobi are stored is called root directory.
4.4.3 Volume Lable and Directories
A labels is a name given to a disk to enable you identify the contents from those of other disks when it’s off-line in that if it’s not mounted on a drive.
Since the use could have multiple disk drives on- line (mounted) at one time, the operating system must have a way of determining when disks are actually mounted on the driver.
To do this, we use volume labels or volume directory, which simply a name assigned to each disk used in the computer installation.
The difference between volume labels identifies a storage medium as physical unit while the latter two identify data stored on disk. Suppose we gave a volume label country to the hierarchy above, the complete name for reaching Milimani file will be: COUNTRY \ KENYA \ NAKURU \ MILIMANI
The operating system will ensure that disk on a volume label Country is located first if it is the one mounted, before it searches for the actual file in the specific directories.
4.4.4 Tab Control
Computers and their operating systems can perform a great number of different tasks, not just one job as say a stand-alone word processor or a calculator. Therefore, the user of the system must be prepared to tell the operating system what particular task to perform at the moment.
When the computer system is complete, usually the application program is what the user communicates with the program when a particular task is desired.
When the application program finishes, it is no longer a part of the system. The user therefore must communicate with the operating systems to tell it what to do next.
He or she does this through the use of what we call OS’s Tab Control Language or TCL. TCL consists of a number of operating system commands also called system commands that control the operating system.
How does one know that the application program has finished its work and it is no longer loaded by the operating system?
The operating system will display that by displaying its prompt; it could be a character or two that will signal the user it awaits further system commands. The MS-DOS Operating System, uses the prompt C: \> or C>. The “C” in the prompt indicates the disk drive in which the operating system will look for any files referred to by the next TCL instructions.
The disk drive attached to the s stem are usually identified by letters of the alphabet through a system with four drives could have drive identifiers A: through D.
Any reference to a drive must include the colon in the drive identifier. The drive identifier displayed by the dos prompt is known as a logged drive, the default drive or the active drive.
4.5 Ms-dos Commands
Using system commands is quite easy.
It is a matter of knowing the right commands key, key it in and press enter key for the command to be accepted.
System commands help us to manage our files and directories for example; we can copy a file from one disk to another, delete files or change names. We can also manage our disks for example to format a disk, label a disk or copy disks.
The Syntax of a Dos Command
The Syntax of a Dos Command A Dos command usually has a command name (i.e the system command the user intends to use) and an argument which is information required by the command.
An argument used with a Dos command will indicate the disk drive on the file to be used by the command Example: COPY ANN 1 TO ANN 2 The command has a command name COPY. The arguments are ANN 1 and ANN 2.
This command copies a file known as ANN 1. The new copy is named ANN 2.
N/B: ANN 1 and ANN 2 are arguments and are separated from each other by a blank space. They are also separated from the command name by a blank space.
4.5.1 Running a Program
It is important to note that a Dos Command represents a program. A command name is just like a file name of any other program. To be able to run a program using Dos, first the operating has to be loaded.
Loading the operating system is simply switching on the computer, it will open a program loaded in ROM to check if the operating system is loaded in drive A or any other and load, other wise it will load from the hard disk.
To run a program with filename extension COM, BAT, TXT, simply enter its filename without the extension for example to a Basic Program simply enter BASIC.
Its filename is BASIC.COM.
When you want to execute a program that is not stored on a disk in the logged drive, the first thing would be to change the logged drive to the disk containing the program.
For example, suppose you wanted to run a program with the filename MILO.EXE which is on the disk in drive B:, and the logged drive is A:, to specify the drive on which Dos should look for the program, proceed with the filename with the drive identified with no blank in between the colon and the filename. B: MILO
4.6 File Management Commands
4.6.1 Changing the Logged Drive
To change the logged drive from the active one, simply enter the letter of the alphabet for the new drive at the prompt of the active drive followed by the colons and then press Enter key.
For example, if the active drive is C:\>, simply type
A: at the prompt and press Enter. C: \ > A: \ > A:\> or A:\>
4.6.2 Determining the Contents of a Diskette
To determine the contents of your disk, Dos provides a program command DIR (Directory) The files are usually listed one per line with their filenames, filename extension, size and If you have many files than can be displayed on the screen, then Dos passes them so program.
There are two solutions to that program: that will display the files stored in your disk with the exception of the hidden files. the date and time they were last saved.
fast over the screen that you cannot be able to read or identify a particular Activate Windows
(i) /P (Pause)
Switch To see the files with all the relevant information ie. filename, filename extension, size and date and time, then /P switch does the work.
The files will be shown one screen at a time and tests the user to see the files with instructions to “press any key to continue…” The format is DIR/P
(ii) /W (Wide)
Switch This command will display filenames and their extension only for the entire directory at once.
They will be displayed in rows five files wide. The format is DIR/W .
- To see only a particular file on Disk Simply use the filename of that file as the argument, thus: DIR B:FILENAME.TXTIn this case, Dos will display the particular information about that file or tell you that it is not on disk.
- To see Direction with similar extensions.If your files have the following extensions; BAS for Basic Programming files, DBS for Database files, to see their directory of all the Basic programming files, enter: DIR*.BAS or DIR/P.BAS or DIR/W*.BAS The asterisk is called a wild card. What it means is that you “substitute the position with any characters.” For instance in the command DIR*.BAS will list all the files with the .BAS extension.
Directory of files with similar names and different extensions Suppose your filenames are the same but have different extensions, all that you need to do is: DIR Same.*
All files called “Same” will be displayed. Suppose you decided to identify your files as Same 1, Same 2 and so on, and therefore you wanted to only display a filename Same but with specific extension DBF, you would enter: DIR Same*.DBF To see all same files you would enter: DIR Same*.*
The asterisk wildcard is a many character wild card. It fills out a filename or extension from its position to the end of the name in the above EXE file, the asterisk is the fifth, sixth, seventh and eighth character if they exist in the filename beginning with SAME.
Another wild card used in the Dos command if? It is usually called a one character wild card. When it appears in a command, you can substitute it with one character e.g. DIR ?AME*.DBF, will substitute ? with any character as long as the next line i.e AME is part of that filename.
So if it is a command, like DIR SAME*??? Would be the same as DIRD SAME*.* when the three questions marks in the former stand fir three character.
4.6.3 Changing Directories
Let us go back to the example we gave with root directory KENYA.
Suppose you wanted to make Hurlin hum your current directory, you simply need to enter to command: CD C: NAIROBI HURLINGHAM. If you are already in C: as the logical drive, you do not need to enter it again, simply type: CD.
If you wanted to move up one level of the directory i.e. to Nairobi, type: CD.. Suppose you were to go straight to the root directory i.e. KENYA, all you need to type in at the prompt is: CD \ If you want to see the sub directory of a current directory, type DIR. .
For e)sample if you have made Nakuru your current directory, to see sub directory like Milimani simply enter the latter command!
4.6.4 Making Directories
Suppose you wanted to make a sub directory of your current directory Nakuru, what you need to do is enter that command MD (Make Directory) and the name you intend to call the sub directory, thus: MD LANGA If towards creating the directory named LANGA you want to work in it, simply use the CD command to place yourself in it, thus: CD LANGA
4.6.5 Removing Directories
To remove a directory, first ensure that the directory to be removed is empty.
You can empty a directory by using DEL command after making back- up copies of the same. To effect the command to remove a directory like NYALI, ensure you place yourself in MOMBASA directory first, thus: CD MOMBASA RD NYALI
4.6.6 Copying a File
It is often necessary to make a copy of a file. All important files should always be copied so as to guard our self against the loss of data.
Data loss often occurs if you accidentally erase a file, Power goes off before you save your files, store data under an incorrect name, do physical damages to a diskette. When you copy a file to protect against loss of data we say you are backing up a file.
The copy command requires 2 parameters/arguments to accomplish the task. It is a resident command.
(i) The first argument is the name of the file to be copied.
(ii) The second argument is the filename for the copy. If the file is not on the logged drive, then drive identification must be included.
4.6.6.1 Copying from the same Drive
Thus: Copy SAMEl.DBF ZAME2.DBF
The above command will copy file named SAME1 on the same drive and give it a new name ZAME2.DBF. it is important to note that if you are copying within the same drive, then the new file must have a different name.
4.6.6.2 Copying from one Drive to another
To copy a file from one drive to another giving it the same name. Enter: COPY SAMEl.DBF B: New file name is not necessary on the target drive (B:) since it is the same as that of the source drive.
4.6.6.3 Copying a range of Files.
To copy a range of files, we employ wildcards for example: Copy same*.*B will copy all files on the logged drive that start with same onto the diskette in drive b: irrespective of filename extension.
To copy the entire contents of drive A: to B, we can use the following command: COPY A:*.*B: N/B: Ensure that the destination diskette is formatted before the operation is started since this command COPY doesn’t copy formatting information as does DISKCOPY command (4.7.4).
4.6.7 Renaming Files For the sake of clarity, the user can rename an old file with a new name.
The command is RENAME or simply REN. The format of this resident DOS command is: At the prompt of the logged drive containing the disk with the old filename type: RENAME OLDNAME.TXT NEWNAME.TXT This DOS internal command will not allow you to change a file name to one already existing in the diskette.
Notice the single space left between the arguments themselves and between Dos command and the argument oldname.
The use of wildcard is important here as they could help rename a wide range of files, for instance: RENAME SAME*.DBF SAME*.WPF This will change all the filename extensions of all the SAME files to Word Processing Files (WPF).
To rename a file on a different drive, you would do this:
RENAME B: SAME.DBF ZAME.DBF to rename a file in B: 4.6.8 Deleting Files Two Dos commands available for deleting files are DEL and ERASE.
The format is: DEL ZAME.DBF This will delete only a file named ZAME.
To delete the entire directory of ZAME (that is plus the subdirectories), enter: DEL *.* That is if you are placed inside the directory ZAME.
4.6.9 To Display the Contents of a File
To be able to sim 1 dis la the contents of a file on the monitor.
The command type is provided. The format is: TYPE Filename.EXT Indicate the filename that is plus extension if you intend to display the contents on the screen.
NB: You can press CTRL + S to stop the contents on the screen from passing too fast for you.
4.6.10 To print the Contents of a File
If you need a hard copy of the contents of a file, then enter the format below:
TYPE Filename.EXT>PRN
N/B: You could also use the command PRESS CTRL + P which will sent everything on the CRT to the printer. To sto rintin re P a. ain.
4.7 Disk Management Commands
Under Disk Management commands, we will examine the following commands: Formatting a Floppy Disk Inserting a Floppy Disk Copying disks p Adding Dos to a formatted disk
4.7.1 Formatting a Diskette
Formatting is a process of preparing new diskettes for data storage. The system command is FOMART.
What formatting does: it organizes the disk so Dos can store data, keep track of them and retrieve them from disk. It also ensures that there are no defective areas on the new disk.
If at all the defective areas are found, FORMAT will mark them so Dos does not store data in them.
Formatting usually takes two ways: A disk can be formatted to include Dos or not.
Disks that include the operating system or Dos are called system disks or boot disk or command disk and can be used to start the computer (or load the operating system).
Disks that do not have the operating system stored in them have more room to store data than the former.
Procedure:
(i) To Format a non system or data disk Simply enter FORMAT followed by a drive identification if the new disk is not to be in the logged drive i.e. FORMAT or FORMAT B: This command will prompt Dos to load format program and display the following message: INSERT NEW DISKETTE FOR DRIVE A: and strike any key when ready.
In the file case or INSERT NEW DISKETTE FOR DRIVE B: and strike any key when ready in the second case.
Simply put the new diskette in the indicated drive and press any key. Dos will display: Formatting … After a few minutes, Dos repeats
Formatting Format Complete 362496 bytes total disk space 362496 bytes available on disk Format another (Y/N)
To which you will answer “Y” or “N” press Y if you want to format another otherwise press N key from the keyboard.
(ii) Formatting a disk so that it includes the systems.
Simply follow the above procedures with addition of letter S for system thus: FORMAT /S or FORMAT/ S B:
The messages displayed are the same as the ones above with addition of the ones indicating that system transferred and how much space it required.
A disk with the system includes some hidden files the names of which do not appear when you look at the contents of the disk, and a file called COMAND.COM.
These files form the resident portion of Dos.
4.7.2 Adding Dos to a Formatted Diskette
Adding Dos to a formatted diskette is a two-step process:
(i) With the target diskette in B: and a system disk in the logged driver, copy the hidden files to the diskette with the SYS command: SYS B: SYS is a non-resident program (or transmit) i.e. it is not kept in RAM. It generates the following messages: SYSTEM TRANSFERRED
(ii) After the above process, copy COMMAND.COM from your system disk t the disk you are modifying by entering COPY COMMAND.COM B:
NB: you can add Dos to any diskette as long as there is enough space to store the three files.
If a disk already has hidden files and you try to use SYS command to place them on the disk anyway, you will get an error message indicting that there is no room on the disk for the system.
The only way to replace the hidden files once installed is only by formatting the disk again.
4.7.3 Labeling a Disk
A volume name is used to identify disks just as you identify them by writing identification information on a label placed on the disk envelope.
The volume name however, is recorded on the disk itself and can be checked by the operating system to ensure that the correct disk has been installed in the disk drive.
Volume label (11 characters; ENTER for None)? MY DISKETTE 362496 bytes total disk space 362496 bytes used by the system 321536 bytes available on disk Format another (Y/N)
A> NB: Always have some formatted disks with you because some application programs will not give the leeway to format a disk while working on it.
4.7.4 Copying Disks
There is a utility called Disk copy that is often provided for in most versions of Ms-Dos and Pc-Dos.
What this utility does is that it copies the entire contents of the source disk to the destination disk.
It also transfers the operating system and formats the destination document as well.
What this utility does not do is to check for errors in the destination disk and mark them so that data is not stored in by the Dos.
While using the cw1i_slcopy command, care must always be taken to clearly identify which disk contains data (i.e. the source disk) and which disk is empty (i.e. the destination disk).
If this is not done, then it is possible to wipe out everything on the source disk because you inadvertently copied the contents of a blank disk to the data disk you intended to reproduce.
Procedure:
The format for DISKCOPY includes two parameters:
(a) Source Drive and
(b) Destination Drive.
To be able to execute the command, enter the following:
DISKCOPY A:B:
This command will copy the contents of the entire drive A: to the one in drive B:. NB: Everything on the disk in B,:,,t the destination drive, will be destroyed by the operation. After the command, Dos will prompt you to insert the disks.
You can as well specify DISKCOPY B:A: if you intend to copy from drive B: to drive A:.
This method is often effective for disks that are full otherwise we would use the command: COPY A:*.*B: To copy all the files in drive A: with any extension to a disk in drive B.
this command as opposed to c_lisccopy, will always check for faulty areas on the destination drive and mark them so that no data is kept in them.
4.8 Summary
✓ An Operating System is a set of program “housed” within the system software that standardizes the way the computer’s resources are made available for the user to applications software.
✓ The functions of an operating system are the following: Memory management, In ut Out ut management, Resource allocation, Error handling, Provision for user interface, hatUfri , File management and Job control.
✓ Operating Systems could be single user of multi user. Ms-Dos commands can be divided into File Management Commands and Disk Management Commands.
Some Dos commands are internal (or resident) and some are external (non-resident or transient) which means they have to be logged first before they can be used.
✓ Examples of file management commands are: Deleting, copying and renaming files, viewing, changing and creating directories.
Examples of Disk Management commands are: Copying disks, labeling disks and formatting disks.
✓ Resident Dos commands include: DIR, COPY and DISKCOPY, RENAME.
✓ Non-resident Dos commands include: FORMAT, SYS.
4.9 Questions
1. Define the term Operating System.
2. State and discuss functions of an Operating System.
3. What are the two types of Operating Systems? Explain.
4. List commands under the following headings:
(i) File management;
(ii) Disk management;
5. What is the syntax of a Dos command?
6. List some of the internal and external Dos commands that you know.
7. What will the following Dos commands do?
(i) COPY DATA 1 DATA 2
(ii) COPY DATA1 B:
(iii) MD DATA 3
(iv) RENAME OLDNAME.TXT NEWNAME.TXT
8. What is a Wildcard? Differentiate between Wildcard and Asterisk ) and (?).
9. Explain what the following Dos Commands will do:
(i) COPY DATA *.*A:
(ii) DISKCOPY A:B:
(iii) DEL DATA*.DBF
(iv) ERASE ?ATA*.*
(v) TYPE DATA*.*
(vi) TYPE DATA*.DBF>PRN
10. () What is formatting?
Why is it important
(ii) How would you format a Diskette?
How can you include an Operating System to a formatted diskette?
(iii) What are the two ways of Adding Dos to a formatted disk?
(iv) Write down the command for Adding Volume Label to Disk.
FREE COMPUTER STUDIES NOTES FORM 1-4
COMPUTER STUDIES NOTES FOR FORM 1-4 COMPLETE
COMPUTER STUDIES NOTES FOR FORM 3 PDF
COMPUTER STUDIES NOTES FOR FORM 1-4
COMPUTER STUDIES NOTES FOR FORM 3 WORD
COMPUTER STUDIES NOTES FOR FORM 4
COMPUTER STUDIES NOTES FOR FORM 2
COMPUTER STUDIES NOTES FOR FORM ONE
COMPUTER STUDIES NOTES FOR FORM 4 EDITABLE
COMPUTER STUDIES NOTES FOR FORM 2 COMPREHENSIVE
COMPUTER STUDIES NOTES FOR FORM 4
COMPUTER STUDIES NOTES FOR FORM 2
COMPUTER STUDIES NOTES FOR FORM 1
COMPUTER STUDIES NOTES FOR FORM 1 OPERATING SYSTEMS
COMPUTER STUDIES NOTES FOR FORM 1 INTRODUCTION
COMPUTER STUDIES NOTES FOR FORM 1 COMPUTER SYSTEMS
COMPUTER STUDIES NOTES FOR FORM 3 PROGRAMMING
COMPUTER STUDIES NOTES FOR FORM 3 SYSTEM DEVELOPMENT
COMPUTER STUDIES NOTES FOR FORM 2 WORD PROCESSORS
COMPUTER STUDIES NOTES FOR FORM 2 DATABASES
COMPUTER STUDIES NOTES FOR FORM 2 DATA SECURITY
COMPUTER STUDIES NOTES FOR FORM 4 APPLICATIONS OF ICT
COMPUTER STUDIES NOTES FOR FORM 1 WORK BOOK
COMPUTER STUDIES NOTES FOR FORM 3 HANDBOOK
COMPUTER STUDIES NOTES FOR FORM 1
COMPUTER STUDIES NOTES FOR FORM 1 SIMPLIFIED
COMPUTER STUDIES NOTES FOR FORM ONE
COMPUTER STUDIES NOTES FOR FORM 2 HANDBOOK
COMPUTER STUDIES NOTES FOR FORM ONE
MORE RELATED DOWNLOADS.
 Form 2 Exam Papers & Marking Schemes
Form 2 Exam Papers & Marking Schemes